Launched in late February, the joint U.S.-Israeli airstrike campaign against Iran (codenamed Operation Epic Fury/Roaring Lion) was quickly met with retaliatory cyberattacks. Iran’s hackers wasted no time launching disruptive operations, including a breach of U.S. medical tech firm Stryker, which reportedly wiped thousands of computers and paralyzed the company’s global operations.
Not only are Iranian state-sponsored threat actors involved, but so are a broad ecosystem of pro-Iran hacktivist groups and even unrelated opportunistic hackers. These actors are targeting a wide range of organizations, from Israeli government agencies and companies to Western enterprises and regional Middle Eastern infrastructure.
While the intensity of activity has temporarily subsided under a fragile ceasefire, recent negotiations between the United States and Iran have failed to produce a lasting agreement, and further escalation is increasingly likely. Don’t wait to become a target. Use this window to take proactive measures, identify exposure, and strengthen defenses before activity ramps up again.
A Surge in Conflict-Driven Cyber Operations
The escalation of military operations triggered a surge in cyber retaliation campaigns. Within hours of the initial strikes on Feb. 28, Iran’s networks went almost dark as Tehran imposed an internet shutdown that temporarily hindered the coordination of its state-aligned hackers.
This gave space for dozens of Iran’s cyber proxies and sympathetic hacktivists to step in and carry the torch. Over the ensuing days, these actors unleashed phishing campaigns, credential theft attempts, espionage intrusions, and malware (including wipers) in the service of Tehran’s cause.
Iranian espionage units like TA453 continued their operations as well. On March 8, TA453 (aka Charming Kitten) was observed phishing a U.S. think tank.
These early patterns are important because they provide a clear preview of how threat actors are likely to operate if the conflict escalates further.
The Hacktivist Ecosystem Supporting Iran
Amid blackouts and technical limitations, pro-Iran hacktivist groups carried the torch for the regime. Over 60 distinct hacktivist collectives have become active since the war began, many coordinating their efforts through Telegram channels called “Electronic Operations Rooms” formed on Feb. 28.
Iran has a long history of operating through deniable cyber proxies, and this playbook is in full effect now. Both the IRGC and MOIS are known to “employ hacktivist personas… with plausible deniability” to conduct attacks on their behalf. This strategy allows Iran to hit back in cyberspace while officially distancing itself from the ops.
These hacktivist fronts often blend state-grade tactics with cybercrime tools to amplify their impact. For example, Handala has deployed repurposed malware from the criminal underground (like the Rhadamanthys information-stealer) alongside custom destructive wipers in its attacks.
If hostilities resume, this decentralized ecosystem allows Iran-aligned actors to quickly re-mobilize and scale attacks with minimal warning.
Key Iran-Aligned Threat Actors
Below is a brief profile of several prominent Iran-aligned threat groups active in this conflict. These range from apparent hacktivists to known state-operated units. Understanding these groups is critical, as they are likely to play a central role for as long as tensions persist and cyber retaliation remains an active component of the conflict:
- Handala Hack Team (Void Manticore): A so-called “hacktivist” persona assessed to be run by Iran’s MOIS. Handala emerged in late 2023 and quickly gained notoriety for destructive attacks and espionage operations.
Its modus operandi includes targeted phishing to gain access, deployment of web shells for persistence, data theft, and finally wiping of systems for maximal damage. Handala communicates via Telegram and operates a leak site where it dumps stolen data as part of hack-and-leak psychological ops. In March 2026, it claimed the high-profile wiper attack on Stryker Corporation as retaliation for strikes on Iran.
The OP Innovate Research Team has done extensive coverage on the Handala group. For more info, please read our full report:
- Cyber Islamic Resistance: An umbrella collective of pro-Iran hacktivist teams coordinating attacks. This group acts as a sort of “joint operations room” for smaller crews (like RipperSec, Cyb3rDrag0nzz, etc.), enabling synchronized campaigns of DDoS, website defacement, and data-wiping attacks against Israeli and Western targets.
- FAD Team (Fatimiyoun Cyber Team): A pro-regime group notable for its focus on destructive and industrial control system (ICS) attacks. FAD Team’s members, aligned with the IRGC’s Fatimiyoun unit, have boasted about breaching SCADA/PLC control systems in Israel and elsewhere.
They allegedly gained unauthorized access to dozens of OT devices at an Israeli security firm and even targeted infrastructure in other countries. The team specializes in wiper malware and permanent data destruction. - Dark Storm Team: A pro-Palestinian/pro-Iran collective that has specialized in large-scale DDoS attacks and ransomware-style extortion. Dark Storm (aka MRHELL112) emerged during the conflict claiming credit for knocking offline Israeli bank websites and other portals via DDoS.
It also engages in data breaches, sometimes posting stolen data with ransom demands (often more for publicity than profit).
Other opportunistic actors: In addition to the above, numerous smaller or transient groups have appeared: APT Iran (also called “Islamic Cyber Resistance in Iraq – 313 Team”), Evil Markhors, Sylhet Gang, Palestine Hackers, and more.
Many of these simply launch nuisance-level attacks (DDoS, defacements) or amplify propaganda. Notably, even pro-Russian hacktivists like NoName057(16) have piggybacked on the conflict narrative, attacking Israeli web targets in solidarity.
Important: The vast majority of hacktivist activity is more about perception than impact. Security experts warn that many of the loud claims made by these groups are exaggerated or outright false. For example, hacktivists have claimed “we breached Israel’s Iron Dome system” or “infiltrated critical infrastructure,” but provide no evidence.
The Conflict’s Global Cyber Fallout
While Israel and Iran are the primary adversaries, the cyber fallout from their conflict is reverberating far beyond their borders. Below we examine how regional allies, Western companies, and even physical infrastructure have been swept up in the digital crossfire – and how entirely unrelated threat actors are exploiting the chaos.
Attacks on Regional Allies
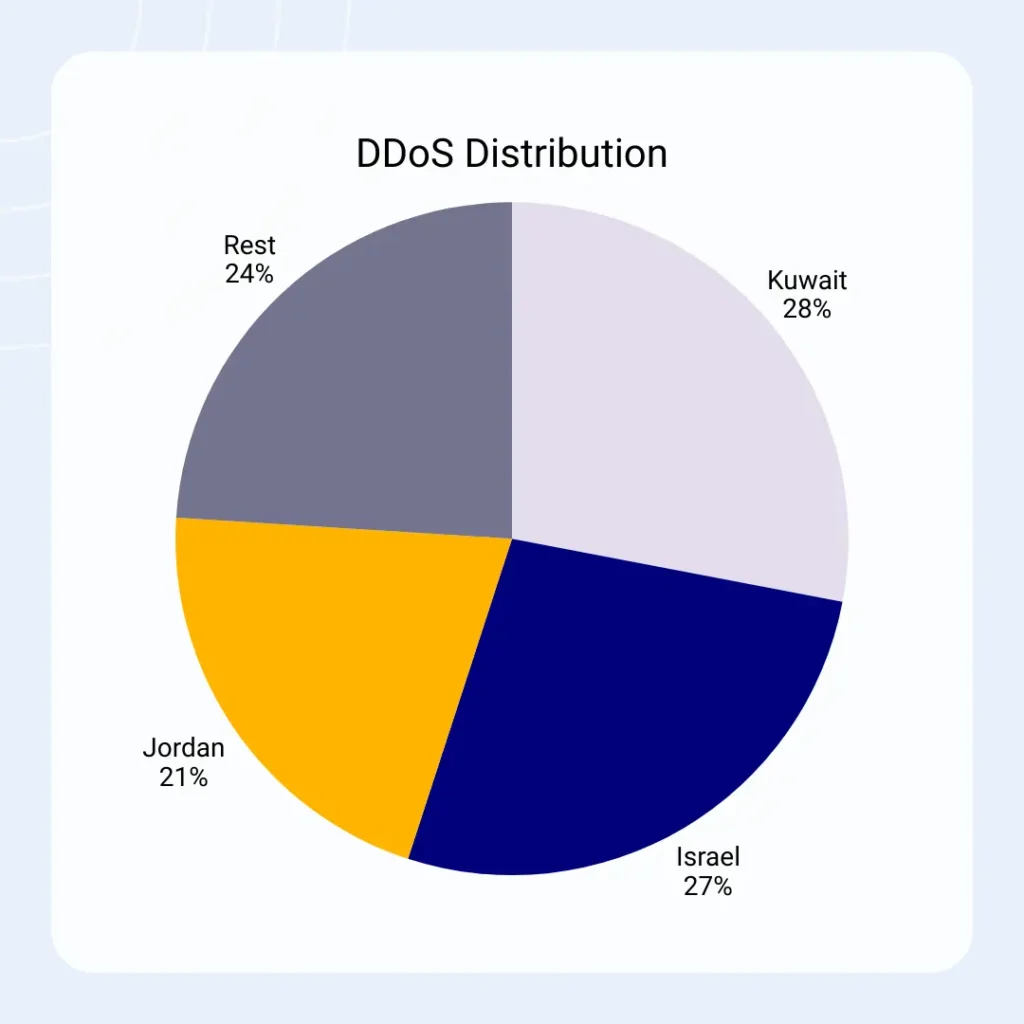
Iran and its supporting hackers have extended their cyber retaliation to countries allied with Israel or hosting U.S. assets in the Middle East. Jordan, Saudi Arabia, the UAE, Bahrain, and Kuwait have all reported being targets of cyber operations linked to the conflict.
Much of this has come in the form of denial-of-service attacks and defacements aimed at government websites and infrastructure. In fact, data shows that in the first days of war, about half of all recorded hacktivist DDoS attacks worldwide targeted the Middle East, with Kuwait (28%), Israel (27%), and Jordan (21%) being the top three by volume.
Western Companies in the Crosshairs
Iran’s cyber retaliation has also taken aim at Western private-sector companies, especially those with real or perceived ties to Israel. The logic is to impose economic pain on Israel’s partners, and second, to signal that anyone doing business linked to Israel could become a target.
We saw this with the massive attack on Stryker Corporation, a U.S.-based medical devices manufacturer, which Iranian hackers characterized as a “Zionist-affiliated” company due to its acquisition of an Israeli firm in 2019.
In the Stryker incident, attackers leveraged admin access to Microsoft Intune to remotely wipe ~200,000 devices, halting production lines and hospital supply shipments overnight.
For many organizations, this means that geographic distance offers little protection if they are even indirectly linked to the conflict. Security experts warn that any organization with Israeli partnerships, operations in Israel, or support for Israeli defense could face similar reprisals.

“Groups like Handala have historically focused on Israeli government, defense, and critical sectors, but that scope is clearly expanding,” said Omer Pinsker, CEO and Founder of OP Innovate. “Over the past year, we’ve seen increased targeting of Gulf States, and we expect that to extend further to U.S. organizations, particularly those with ties to Israel or embedded in Israeli supply chains. For many Western companies, that effectively puts them in the line of fire.”
Critical Infrastructure and Cyber-Physical Convergence
Perhaps the most sobering development in this conflict is the blending of cyber and physical warfare. Iran has not hesitated to cross the threshold into kinetic attacks on digital infrastructure, effectively treating data centers and networks as fair game for missiles and drones.
On March 1, the IRGC launched drone strikes against Amazon Web Services (AWS) cloud data centers in the UAE and Bahrain, causing power outages and triggering fire suppression systems. Analysts noted the intent was to “inflict maximum global economic pain” by disabling cloud services relied on worldwide.
What This Means for Security Teams
For security teams worldwide, this conflict underscores a new reality: geopolitical flare-ups now translate to immediate cyber risk for organizations, regardless of location. The old notion that only governments or critical infrastructure need worry about nation-state hackers doesn’t hold anymore. As we’ve seen, a hospital supplier in the US, a telecom in France, or a bank in the UAE can all become targets or collateral damage when cyber warfare ramps up.
Concretely, organizations should assume a period of heightened phishing and social engineering threats. The volume of war-themed phishing emails, texts, and scams is dramatically elevated – attackers know people are anxious and hungry for information, making them more susceptible. Expect everything from spoofed news alerts and fake charity appeals to highly targeted spear-phishing that name-drops the conflict to build credibility.
Defensive Measures Organizations Should Prioritize
In light of the threats described, companies should take proactive steps to shore up their defenses. The goal is to both raise the barrier to entry for attackers (prevent breaches) and mitigate damage if an incident occurs. Below are key measures OP Innovate recommends:
- Reduce External Attack Surface: Make it as hard as possible for attackers to find a way in from the internet. Ensure all internet-facing assets are fully patched and up-to-date (VPN gateways, web servers, etc.), as Iranian actors routinely exploit unpatched systems and default credentials. Consider temporarily taking non-essential portals offline if they aren’t needed during this high-risk period.
Also, harden remote access points. For example, require VPN authentication for admin interfaces or restrict them by IP. As Zscaler ThreatLabz advises, “make apps (and vulnerable VPNs) invisible to the internet” so that attackers simply can’t reach them.
To easily identify all external attack surfaces, exposed assets, and misconfigurations before attackers do, contact us for a live demo of OP Innovate’s WASP platform.
- Strengthen Identity Security: Many of the most devastating attacks (e.g. the Stryker wiper) began with stolen credentials and abuse of legitimate admin tools. It’s imperative to implement phishing-resistant multi-factor authentication for all user and administrator accounts.
Basic SMS or app-based OTPs may not suffice, as adversary-in-the-middle phishing kits can hijack those sessions. Whenever possible, use FIDO2 security keys or other MFA that verifies the login origin.
Beyond MFA, enable policies like immediate alerting on new device enrollments or email forwarding rule changes (common signs of account takeover). - Improve Detection and Monitoring: Given the likelihood of increased intrusion attempts and the possibility of stealthy actors hiding amidst the noise, robust monitoring is vital.
Tune your SIEM and EDR systems to look for the TTPs emerging from this conflict – e.g. mass account lockouts or Intune device wipe commands (as seen with Handala), unusual VPN logins from new locations, or the presence of known IoCs like the malicious domains and hashes reported by threat intel.
Subscribe to threat intelligence feeds specific to this conflict (many vendors are sharing updates on indicators related to Iran and hacktivist activity). It’s also wise to actively hunt in your environment for any silent footholds or data staging. - Train Employees Against Conflict-Themed Phishing: User awareness is often the best last line of defense in phishing scenarios. Take this opportunity to educate your workforce about the specific lures they might see related to the Israel-Iran war.
For example, employees should be wary of unsolicited emails referencing emergency updates, donation requests for war victims, or anything urging immediate action “due to the conflict.” Run targeted phishing simulation tests with war-themed scenarios to gauge your exposure.
Evaluate Supply Chain Risk: Lastly, take a hard look at your third-party connections and dependencies. As noted, Iranian attackers are not just going after primary targets but also those targets’ suppliers, contractors, and software providers.
Review which vendors and partners have network access or hold sensitive data, and make sure their security posture is sound. You may need to temporarily limit third-party integrations or apply extra monitoring to them during this high-threat period.
Communicate with key suppliers about the steps they’re taking (for instance, ask your MSP or cloud provider about their heightened security measures).
Also, plan for the scenario where a critical provider (cloud host, SaaS app, etc.) is knocked offline due to a cyber incident. Do you have backups or alternative services if, say, a major data center in your region goes down?
Protect Your Business With OP Innovate
In times of heightened nation-state threats, having expert support at your side can make all the difference. OP Innovate is uniquely positioned to help organizations stay secure amid conflicts like the current Israel-Iran cyber clash.
Our team brings extensive experience in handling advanced persistent threats and state-sponsored incidents, including direct experience countering Iranian-linked attacks. We offer immediate Incident Response assistance to contain and eradicate intrusions, as well as proactive “Exposure Assessments” to identify where your business might be vulnerable before an attacker finds the gap.
OP Innovate’s proprietary WASP platform (Web Application & Service Protection) provides continuous monitoring of your external attack surface and real-time validation of your security controls.
For more information and a live demo of WASP, please contact our team.