As a CISO, CTO, or security leader, you understand the value of regular penetration testing. However, as your company scales and your security program matures, the pentest provider that once met your needs might now be holding you back.
In an era of agile development and evolving threats, a “one-size-fits-all” pentest vendor can become a liability. Below are five telltale signs that your organization has outgrown its current penetration testing provider.
Each sign highlights a common pain point for mature or scaling companies and is backed by industry insights. If you recognize these in your own operations, it may be time to seek a more advanced and adaptive pentesting partnership.
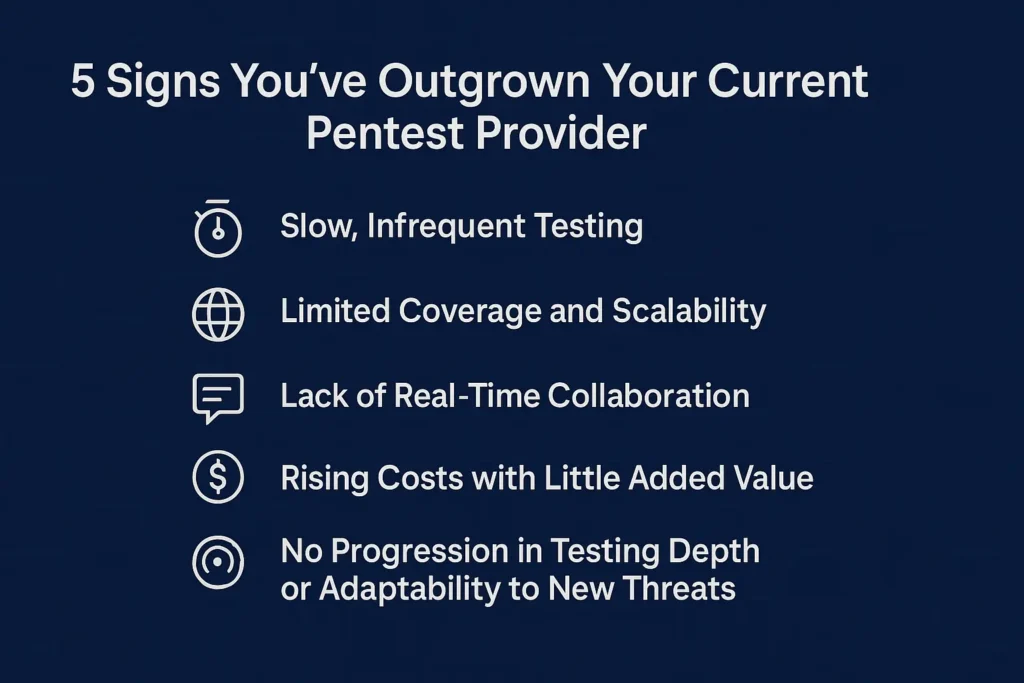
1. Slow, Infrequent Testing
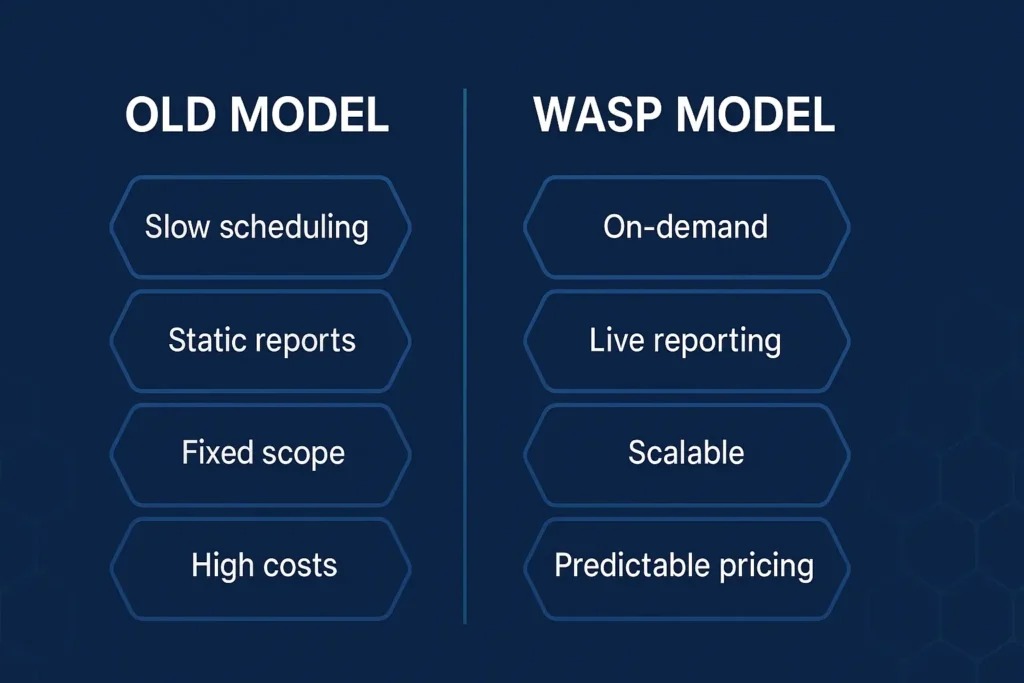
In a fast-paced DevOps environment, waiting weeks or months for a scheduled pentest is untenable. If your provider requires extensive lead time and only delivers point-in-time assessments infrequently, you’ve likely outgrown them. Traditional consultancies often follow an “engage, execute, and exit” model with long gaps between tests.
So, by the time a static PDF report arrives, your applications or network may have already changed, leaving newly introduced vulnerabilities untested. Modern organizations releasing code weekly or even daily need security testing that keeps up. Experts note that in agile environments, continuous, iterative testing isn’t possible with traditional models, as you only get a snapshot of risks at a given moment
Mature security programs are shifting toward more frequent testing. Industry surveys show many companies are moving to quarterly or even monthly tests rather than annual ones. When your current provider cannot support that frequency and agility, your organization’s security may lag behind development, leaving you exposed between tests.
2. Limited Coverage and Scalability
Another clear sign of outgrowing a pentest vendor is when your environment’s complexity and scale have surpassed the provider’s capacity or expertise. If your vendor struggles to cover all your critical systems or cannot provide specialists for niche areas (like IoT, OT, or specific cloud configurations), you’re not getting the depth of coverage a mature organization requires.
Additionally, scaling up testing shouldn’t mean scaling up headaches. Ask yourself: Are you finding it hard to schedule multiple concurrent tests for different teams or regions due to your vendor’s bandwidth limits? Traditional penetration testing approaches do not easily adjust to changes in scope or frequency. They simply “do not scale” well for growing companies.
A small boutique firm with only a handful of pentesters might have served you well early on, but as you’ve grown, that limited pool of talent can result in repeated perspectives and missed vulnerabilities. It’s no surprise that organizations historically felt the need to rotate providers just to get “new eyes,” especially if a vendor only had 5 testers on staff.
Modern Pentesting-as-a-Service (PTaaS) providers emphasize on-demand elasticity aka the ability to spin up tests quickly and cover expansive scopes, something your current vendor may not offer.
3. Lack of Real-Time Collaboration
Mature security programs don’t treat pentesting as a one-off project; they integrate it into the software lifecycle. If your current pentest vendor still operates in a silo with minimal collaboration during testing and no integration into your issue tracking or DevSecOps tools, you’ve likely outgrown their approach.
A telltale sign is the dreaded static PDF report that arrives at the end of an engagement with a long list of findings. Not only do such after-the-fact reports risk being stale, but they also force your development team into a reactive mode. Industry experts criticize this traditional model for providing limited interaction between testers and clients and delaying vulnerability disclosure (thus extending your exposure window).
In contrast, modern providers offer real-time reporting portals and closer teamwork between your staff and the testers. For example, with a collaborative pentest platform, developers can start seeing found vulnerabilities from day one and begin remediation immediately, rather than waiting weeks for a final report.
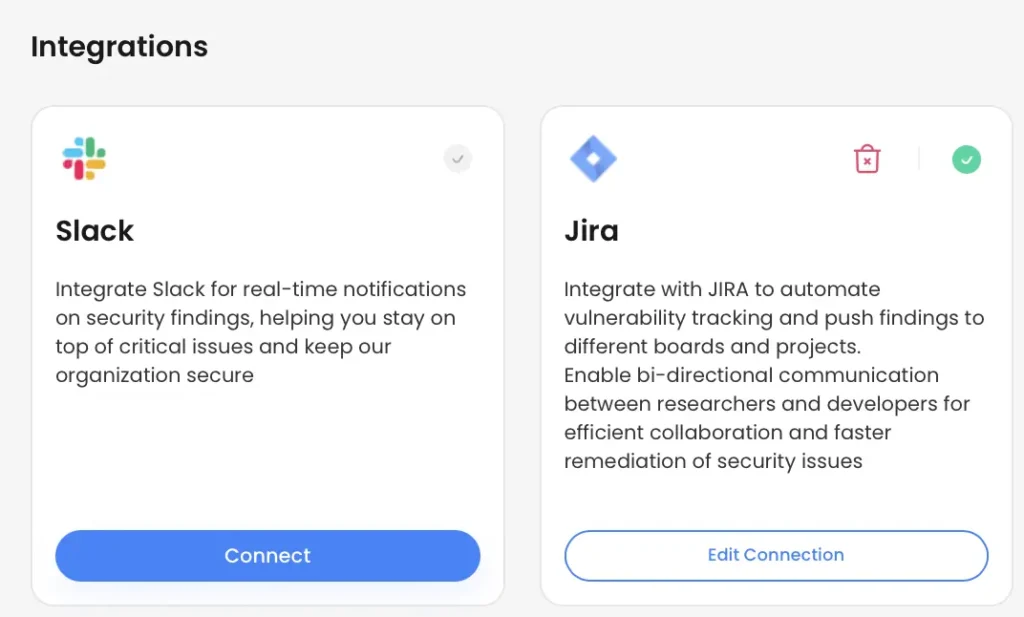
WASP integrates seamlessly with Slack, Jira, email, and custom workflows, delivering findings directly to the tools your team already uses
4. Rising Costs with Little Added Value (Poor ROI on Pentesting)
As organizations grow, so do their pentesting requirements. But that shouldn’t mean costs spiral out of control without commensurate benefits. If you’re pouring more budget into pentests and mainly getting basic findings or compliance checklists in return, it’s a sign your current provider’s value proposition has plateaued.
Traditional pentesting by consultants tends to be expensive, owing to manual effort and overhead, and these costs make truly continuous testing hard to justify. Many security leaders are now tasked to “do more with less,” consolidating spending and demanding better ROI from vendors.
If each engagement’s cost is high and yet you’re not seeing significant new insights or risk reduction, the value is questionable. Modern approaches like PTaaS often tout more predictable, subscription-style pricing and efficient testing processes that drive costs down by automating routine tasks.
They also frequently include features like free retests or continuous vulnerability scanning as part of the package, enhancing value. By contrast, an outgrown provider might charge extra for every little scope increase or retest, and you might find yourself limiting the frequency of tests due to budget concerns.
High-quality pentesting will certainly require investment, but it should also yield actionable risk reduction, not just reports.
5. No Progression in Testing Depth or Adaptability to New Threats
Finally, a more subtle but impactful sign is when your pentesting engagements feel repetitive, and the provider isn’t helping you advance to the next level of security testing. In a mature security program, the goal is not just to find low-hanging fruit each time, but to continuously raise the bar and uncover deeper issues, test new scenarios, and adapt to emerging threats.
If your current pentest vendor keeps running the same playbook year after year, you’ll notice diminishing returns. Perhaps the first couple of tests found critical gaps, but now each test yields only minor issues (or even zero findings) without much context on how to further strengthen your defenses.
On one hand, fewer findings can mean your defenses improved; on the other hand, it could indicate that the testing hasn’t evolved to challenge your now-hardened systems. Security experts caution that attackers are constantly refining their techniques, so your testing approach should do the same.
WASP: Penetration Testing That Sees What Others Miss
Outgrowing a pentest provider is a natural part of an organization’s security journey. The very fact that you’re noticing these pain points means your security program has matured – and now needs a more capable partner. Rather than settling for slow turnarounds, limited scope, and routine reports, you can choose a provider that offers agility, scale, and true expertise.
OP Innovate’s WASP platform combines cutting-edge automation with the creativity and persistence of our seasoned red team professionals who think like adversaries and look where others don’t. This unique blend ensures deep, adaptive testing that goes beyond surface-level checks to uncover vulnerabilities that traditional methods often overlook.
The result is a pentesting program that evolves with your environment, scales with your needs, and provides actionable insights you can trust.
Reach out to OP Innovate to discover how our automation-plus-expert approach can elevate your penetration testing program and help you stay ahead of even the most elusive threats.
Alternatively, you can create your WASP account today for free and experience firsthand how effortless, continuous, and insight-driven penetration testing can be.