
Cyber Incident Response Services
Contain and recover from cyber attacks swiftly and effectively 24/7
Learn More
Incident Response for a multitude of scenarios
OP Innovate's season incident response team can help your organisation resolve a multitude of different attack types and scenarios

Ransomware (Encryption)
Quickly recover from even the most sophisticated ransomware attacks. Contain the threat, determine root cause, window of compromise, attacker activity, and quantify sensitive information exposed. Where required, negotiate with threat actors, acquire and validate decryption keys, and develop and implement a recovery plan.

Business Email Compromise (BEC)
Recover from unauthorized access to your enterprise email environment. Contain the incident, determine root cause, window of compromise, attacker activity, and quantify sensitive information exposed.

Web Application Compromise
Recover from a web application attack. Contain the threat, analyze logs, review code, quantify exposure or loss of sensitive information, and get recommendations for design hardening countermeasures

Insider Threat
Investigate abuse of privileged access afforded to otherwise trusted employees, including identification of data accessed or misappropriated and/or unwanted actions taken by insiders.

Unauthorized Access
Hunt for historical or ongoing indicators of compromise to identify evidence of unauthorized access or activity (across cloud, email, endpoints).

Malware
Analyze malware samples using open source intel, sandboxing, reverse engineering, and deliver a report, including the behavior and functionality of the malware.
Be Prepared for any cyber attack with ANT Rapid Response Tool
Our incident response process gets a critical head start with the ANT rapid response tool.
ANT provides critical network information on DFIR activities from the earliest moments of the team's engagement.
Coupled together, ANT and our IR team can keep you prepared for a swift response to even the most advance cyber attacks



Our track record
with incident response in cybersecurity

Over 10,000 incident response hours performed in the last 3 years alone

100% satisfied customers exceeding expectations

Experience with all types of cyber incidents

Resolving over 50 cyber incidents every year


Gain Access to all key Stakeholders needed for Incident Response
Our innovative framework includes more than just the technical specialists. In our war room you’ll find a variety of disciplines
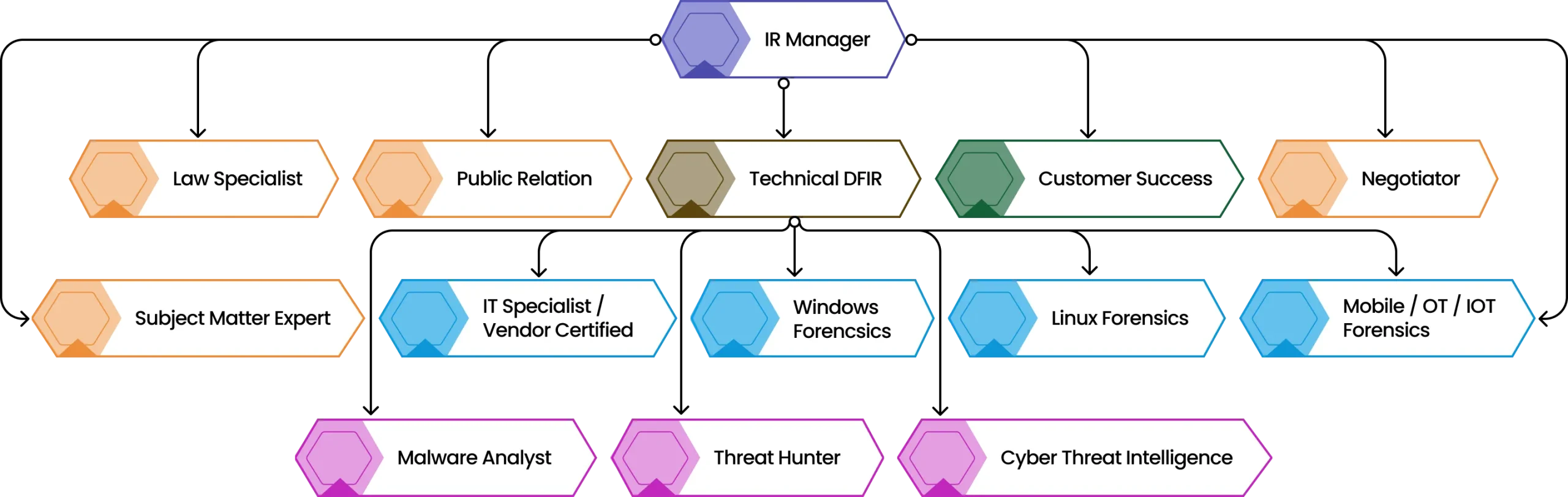





IR Manager -A certified professional with deep expertise in cybersecurity and business analysis. The Incident Response Manager acts as the primary liaison for key customer decision-makers.

Threat Hunter - An offensive security strategist killed in leading offensive operations, capable of tracking and analyzing the steps of attackers.

CTI Specialist - The cyber threat intelligence (CTI) specialist enhances our incident response team by providing critical insights into attacker profiles, interpreting relevant data about the client and their environment.

Crisis Negotiator - Even if your organization doesn’t plan to pay ransom, the negotiator should engage the attacker early to mitigate damage, gather intelligence, and slow their progress to buy time.

PR - Effectively communicating the situation to your customers is crucial for maintaining trust. Our PR specialist ensures that the message of an attack is delivered carefully to avoid sudden drops in stock value.










Accreddited Professionals in Digital Forensics and Incident Response (DFIR)
Certifications
Our team members are all accredited professionals, certified on a variety of sought-after qualifications.
Most of our team SANS GCIH - GIAC Certified Incident Handlers, also holding Practical Malware Analysis qualifications and are OSINT specialists. Their extensive training and experience ensure a rapid and efficient response to incidents, with an unrivaled track record. Our results speak for themselves.










A few examples of some of the customers we've helped recently


Learn how an Incident Response retainer can improve response time and reduce cost
Having a fully prepared incident response plan greatly reduces response time and cost, not to mention unecessary stress. Don't wait for a cyber attack. Receive reduced IR rates and improved response time with an IR retainer

FAQ
Related Resources
15 Vulnerabilities In 11 Elementor Addons Hit +3M WordPress Sites
15 vulnerabilities in 11 Elementor add-on plugins, impacting over 3 million WordPress sites. Key concerns include a high-threat LFI vulnerability in ElementsKit and numerous XSS…
Read more >

CISA Expands Known Exploited Vulnerabilities Catalog with New Entries (CVE-2023-48788, CVE-2021-44529 and CVE-2019-7256)
CISA adds three actively exploited vulnerabilities to its catalog: CVE-2023-48788 (Fortinet), CVE-2021-44529 (Ivanti), and CVE-2019-7256 (Nice Linear), urging prompt patching to mitigate risks of SQL…
Read more >

Remote Code Execution Vulnerability in Ivanti Sentry Patched (CVE-2023-41724)
Ivanti has released patches for a critical vulnerability (CVE-2023-41724) in Standalone Sentry, affecting versions 9.17.0 to 9.19.0. The flaw, with a CVSS score of 9.6,…
Read more >

SQL Injection Vulnerability (CVE-2024-1597) in Bamboo Data Center and Server Patched by Atlassian
Atlassian has patched a critical vulnerability in Bamboo Data Center and Server, designated CVE-2024-1597, with a CVSS score of 10.0, indicating severe risk. This SQL…
Read more >

Urgent Alert: New Vulnerabilities in Mozilla Firefox and Thunderbird
Mozilla has issued urgent security updates for Firefox and Thunderbird due to 14 newly discovered vulnerabilities. These include a high-severity vulnerability (CVE-2024-2615) that allows for…
Read more >

Cisa: Adobe Releases Security Updates for Multiple Products to Address Critical Vulnerabilities
Adobe has released security updates for products including Adobe Experience Manager, Premiere Pro, ColdFusion, Bridge, Lightroom, and Animate to address critical vulnerabilities. CISA urges users…
Read more >

What is an Incident Response ?
Uncover your most critical vulnerabilities and logic flaws before an attacker does. Based on OWASP top 10, test for exploits in web applications, APIs, and thick client apps, leveraging attackers' Tactics, Techniques, and Procedures (TTPs).

Efficient Scans
PTaaS utilizes automated scanning tools to efficiently identify vulnerabilities in web applications, APIs, and network/cloud devices. This saves time and effort compared to manual scanning processes.


Expert Analysis
The human assessment aspect of PTaaS involves security experts with industry accreditations who analyze the results of the scans. Their expertise enhances the detection of complex vulnerabilities and provides critical insight and analysis.


Risk Prioritization
PTaaS not only identifies vulnerabilities but also validates and rates their risk against risk databases. This risk-based approach allows organizations to prioritize remediation efforts and focus on addressing the most severe vulnerabilities first, providing you and your product team with the best return on PT investment over time.

