Go beyond traditional pen testing and simulate real-world attacks with our expert Red Team. Put your defences to the test with a comprehensive red teaming assessment.
Red Teaming: Reveal Your Security Blind Spots
GET STARTEDTraditional pen testing offers a valuable snapshot, but today's dynamic threat landscape demands a deeper understanding. OP Innovate's Red Teaming service simulates real-world attacks from a determined adversary's perspective, providing a comprehensive evaluation of your organization's true security posture.

OP Innovate’s Approach of Red Teaming:
Our Red Team exercises mimic the tactics, techniques, and procedures (TTPs) of real-world attackers, uncovering vulnerabilities across your entire infrastructure, applications, and personnel. We follow a structured methodology, progressing through various stages:


Attack Surface Mapping
We meticulously map your internet-facing assets, software stack, and security controls to identify potential entry points.

External Penetration Testing
We leverage the collected intelligence to exploit vulnerabilities and breach your network perimeter, testing your firewalls, VPNs, office Wi-Fi, and other defensive measures.

Insider Threat Simulation
We mimic both low-privileged and high-privileged insider attacks, targeting your corporate applications, internal systems, and sensitive data.


Lateral Movement & Data Exfiltration
We simulate internal network navigation and data theft, mirroring real-world attacker behavior.


Final Report & Remediation
We deliver a detailed report outlining discovered vulnerabilities, exploitation methods, and actionable recommendations for mitigation. We even offer 1-on-1 communication with your IT team to expedite the patching process.
Red Teaming vs. Penetration Testing: Unveil Your True Security Posture
Aspect | Red Teaming | Penetration Testing |
|---|---|---|
Simulate real-world attacks to assess overall security posture | Identify vulnerabilities in specific systems, networks, or applications | |
Wide-ranging, involving multiple attack vectors | Targeted, focused on specific systems or scenarios | |
Mimics attacker behavior to test defenses and incident response | Uses predefined methods to find and exploit vulnerabilities within a set scope | |
High-level expertise in offensive cybersecurity | Can be conducted by both internal and external security professionals | |
Long-term engagements (weeks to months) | Short-term engagements (days to weeks) |


Choose the right approach for your needs:
Red Teaming: Uncover hidden vulnerabilities and test your entire security posture against real-world threats.
Penetration Testing: Identify specific vulnerabilities in critical systems and applications.
Contact OP Innovate today and schedule your Red Teaming exercise for a comprehensive security assessment.
Get A Free ConsultationWhy Choose OP Innovate's Red Teaming?
Go beyond basic penetration testing and expose blind spots traditional methods might miss.
Evaluate your team's preparedness and identify areas for improvement in responding to real-world attacks.
Gain valuable insights into your overall security posture and make informed decisions to strengthen your defenses.
Benefit from the experience and knowledge of our highly skilled and certified Red Team professionals.

Ready to Test Your
True Security Posture?
Contact OP Innovate today and schedule your Red Teaming exercise.
start now
Trusted by

Related Resources
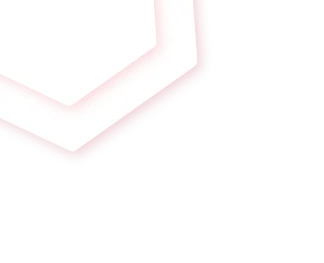
Understanding PTaaS Platforms: Penetration Testing as a Service Explained
Penetration testing is an essential component of an organization’s cybersecurity program. But the periodic snapshots that traditional testing provides are no longer effective in the…
Read more >

Maximizing Web App Security: The Powerful Synergy of ASM and Penetration Testing
According to Verizon’s 2024 Data Breach Investigation Report, nearly 40% of cybersecurity incidents result from web application vulnerabilities. Businesses relying on these applications for everyday…
Read more >

High-Risk Vulnerabilities in the Veeam Backup & Replication Data Storage Solution
Veeam Backup & Replication, a critical data storage and backup solution used by organizations worldwide, has been found to contain multiple high-risk vulnerabilities. These vulnerabilities…
Read more >
Critical RCE Risk in WordPress Advanced File Manager Plugin (CVE-2024-11391)
A critical vulnerability (CVE-2024-11391) has been identified in the Advanced File Manager plugin for WordPress, affecting versions up to and including 5.2.10. This flaw allows…
Read more >
How Penetration Testing Addresses Supply Chain Security Risk
Remember the SolarWinds attack? In 2020, hackers exploited vulnerabilities in the popular IT service management software and injected malicious code in a routine update. 30,000 …
Read more >

CVE-2024-5921: GlobalProtect App Vulnerability
CVE-2024-5921: Critical vulnerability in Palo Alto Networks’ GlobalProtect app allows unauthorized root certificate installation and malware deployment—update to secure versions immediately
Read more >