Active Directory interconnects users, devices, and servers in an enterprise, making it a high-value target for attackers. A breach in AD can grant adversaries the “keys to the kingdom.”
Active Directory remains the backbone of authentication for over 90% of large enterprises. This is especially true in critical infrastructure sectors like utilities, healthcare, energy, where an AD compromise can disrupt essential services and put public safety at risk.
Attackers focus on AD because a single breach can grant them unrestricted access across the entire network. Once inside, they can impersonate users and admins, control devices, and move laterally while blending in with normal operations.
Traditional security tools often struggle to detect these intrusions because malicious AD actions appear legitimate, allowing attackers to persist for months. The average AD breach isn’t detected for over 200 days.
Why Attackers Target Active Directory
AD serves as the central gatekeeper for identity and access in an organization. When adversaries compromise Active Directory, they essentially own the enterprise network. With domain administrator privileges, an attacker can create backdoor accounts, modify group memberships, reset passwords, disable security controls, and push malware through login scripts without raising immediate red flags. In other words, compromising AD lets attackers operate as if they are the IT admins.
During red teaming engagements, OP Innovate regularly uncovers AD misconfigurations and privilege escalation paths that allow simulated adversaries to go from an unprivileged user to full domain compromise in a matter of hours.
And actual attackers are exploiting these flaws too. In 2025, the Marks & Spencer breach showed how quickly identity weaknesses can collapse an environment. After social-engineering the service desk to reset an employee’s password, the attackers exfiltrated the NTDS.dit Active Directory database, cracked the hashes offline, escalated to domain admin, and ultimately deployed ransomware across the VMware ESXi estate, all driven by gaps in AD hygiene and privilege management.
With AD access, attackers can leverage well-known techniques to maintain and deepen their control. Some common Active Directory attack techniques include:
- Golden Ticket attacks: Forging Kerberos ticket-granting tickets (TGTs) that grant essentially unlimited access to the domain for an extended period. This allows attackers to persist as privileged users even if passwords are changed.
- DCSync attacks: Abusing replication permissions to impersonate a domain controller and pull password hashes for any user from Active Directory. In effect, the attacker tricks AD into handing over the keys to all user accounts.
- Kerberoasting: Requesting service tickets for SPN-configured service accounts and cracking those ticket hashes offline to retrieve plaintext passwords. This often targets service accounts that have weak passwords, yielding administrative access.
- Pass-the-Hash/Relay: Exploiting legacy authentication (NTLM, LM) to reuse stolen password hashes or relay credentials without cracking them. If systems don’t enforce modern protocol protections, an attacker can authenticate as a user or admin on other hosts using captured hashes.
These techniques often appear as normal AD traffic, making them hard to spot. An attacker generating a Golden Ticket, for instance, is essentially just performing Kerberos authentication, which is nothing obviously malicious on the surface.
Hybrid Environments Expand the Attack Surface
The move toward cloud and hybrid IT environments has made AD even harder to secure. Organizations now often run hybrid Active Directory setups that sync on-premises AD with cloud services like Azure AD. While this extends the convenience of single sign-on and unified identities, it also expands the attack surface.
A weakness in the cloud side can be a stepping stone into on-prem AD, or vice versa. Attackers have learned to exploit these trust links, for example, by stealing OAuth tokens from a cloud application to impersonate a synced account and then gaining on-prem access.
Additionally, legacy protocols left enabled for compatibility can introduce hidden dangers. Old authentication protocols like NTLM or WMI that remain active in many environments give intruders opportunities for relay attacks and pass-the-hash exploits`.
Microsoft recommends disabling such legacy protocols, but critical infrastructure companies often have older systems that still rely on them. This creates an uneasy trade-off between compatibility and security, and attackers will happily target any lingering outdated services.
Fragmented Monitoring Creates Blind Spots
Another challenge is the fragmentation of security oversight. Cloud identity services and on-prem AD might be handled by different teams with different tooling. An attacker hopping from cloud to on-prem (or vice versa) can slip through the cracks if the security monitoring isn’t unified.
In fact, many organizations struggle to correlate suspicious events across hybrid environments. Threat actors take advantage of these blind spots, knowing that a misconfigured Azure AD Connect or an overlooked admin portal could be their gateway in.
Common Active Directory Vulnerabilities and Misconfigurations
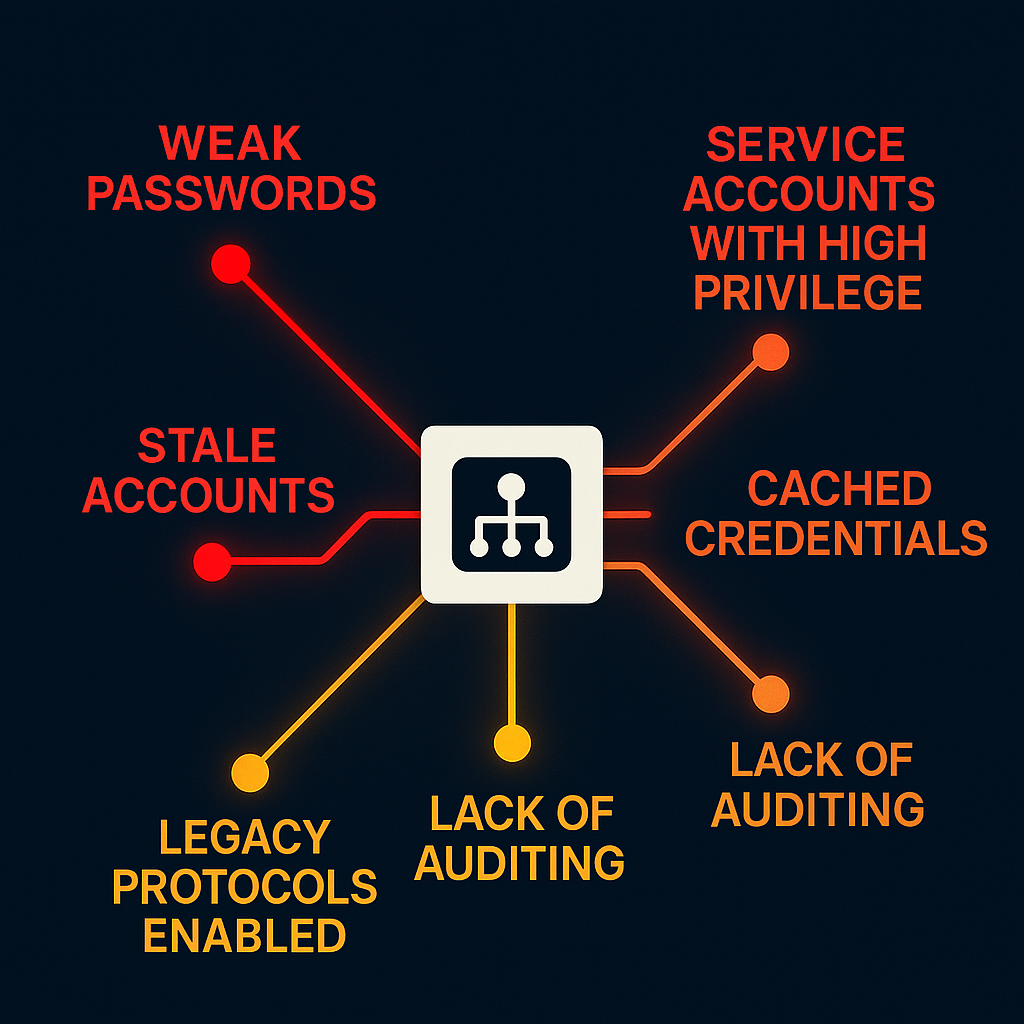
The human element and configuration weaknesses play a huge role in AD breaches. A staggering share of breaches begin with compromised passwords. Verizon’s Data Breach Investigations Report found that stolen credentials were implicated in 88% of breaches.
Attackers have no shortage of methods to obtain credentials: phishing campaigns trick users into giving up passwords, malware like keyloggers steal them, brute-force attacks guess weak passwords, and billions of leaked credentials are readily available on the dark web.
Unfortunately, many enterprises still rely on ancient password practices. Users often reuse passwords across personal and work accounts, meaning a breach of a random website can expose an employee’s AD credentials. Even supposedly “complex” passwords (eight characters with a mix of letters/numbers) can be cracked in seconds with modern GPU rigs. Weak password policy is effectively an open door to Active Directory.
Inside the network, common AD misconfigurations give attackers even more advantages. One frequent issue is over-privileged or unmanaged service accounts. These accounts (used for running services or scheduled tasks) often have passwords that never expire and excessive domain privileges. An attacker who cracks or steals a service account credential can roam freely, since those accounts are rarely monitored.
Another problem is credential caching on workstations. When admins log into a PC or server, their domain credentials may be stored in memory or in local caches. Attackers with a foothold on that machine can extract those cached admin hashes with standard tools, effectively doing an instant privilege escalation. Tools like Mimikatz make it trivial to harvest such credentials from memory.
Lack of AD Governance and Oversight
Organizations also tend to lack visibility and oversight in their AD environments. It’s often unclear how many privileged accounts exist, who is using them, and for what purpose. This opacity means dangerous changes (like a new user being added to the Domain Admins group) can go unnoticed until it’s too late.
Equally concerning is the accumulation of stale accounts (users or admins who left the company but still have enabled AD accounts or credentials that were never revoked.) Attackers absolutely love finding a neglected admin account, and without routine auditing, these vulnerabilities persist in AD for months or years.
The Ongoing Risk of AD Zero-Days
To make matters worse, new zero-day vulnerabilities in Active Directory components are still being discovered. In April 2025, for instance, Microsoft disclosed a critical AD flaw that allowed a low-privileged user to escalate privileges to SYSTEM level on domain controllers. This means that an attacker with just a basic foothold on the network could exploit it to instantly gain domain admin control.
While patches are released quickly, many organizations struggle to roll them out fast enough across all their domain controllers. The window between a patch release and actual deployment is a golden opportunity for attackers.
How to Strengthen Active Directory Security
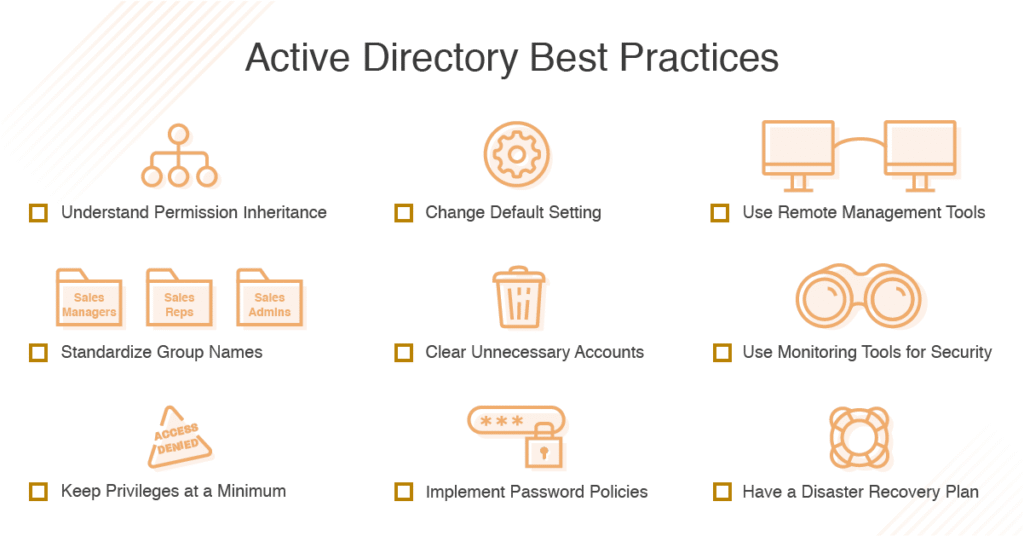
Here are some best practices and strategies to fortify your Active Directory:
Enforce strong passwords and multi-factor authentication (MFA):
Given that compromised credentials underlie most breaches, ensuring users have strong, unique passwords (and rotating them regularly) is essential. Implement robust password policies that block commonly used or breached passwords. Users should not be able to use passwords found in leak databases.
Pair this with multi-factor authentication on all privileged accounts and any remote access points. MFA adds a critical extra layer so that even if an attacker steals a password, they can’t easily reuse it to access AD.
Adopt a Zero-Trust approach:
In an AD context, zero trust means never assuming any user or device is trustworthy by default. Every login and resource request should be evaluated for risk. Implement conditional access policies that check factors like user role, location, device security posture, and behavior anomalies each time before granting access.
For example, if an employee who usually logs in from Tel Aviv suddenly tries to access the VPN from overseas at 3 AM, that should be flagged or challenged.
Keep systems patched and eliminate legacy flaws:
A rigorous patch management program is non-negotiable for Active Directory environments. Apply security updates to domain controllers and critical servers within days, not weeks, since attackers actively scan for unpatched vulnerabilities.
Develop a process to rapidly test and roll out Microsoft’s Patch Tuesday fixes for any AD-related components. In addition, reduce your exposure by turning off features you don’t need. Disable legacy protocols like NTLM or WINS/NetBIOS if your systems can function without them.
Continuous monitoring and anomaly detection:
Given how stealthy AD attacks can be, organizations need real-time visibility into AD events. Deploy monitoring solutions or enable auditing to track every important change in Active Directory. This includes the creation of new users or groups, modifications to roles and permissions, changes to Group Policy, unusual authentication patterns, etc..
Set up alerting for red-flag activities, such as a deactivated account becoming active, a sudden flood of password reset attempts, or replication requests coming from a non-DC machine.
Perform regular audits and penetration testing:
It’s crucial to regularly assess your Active Directory’s security posture just as you would test physical infrastructure. Conduct periodic AD security audits or have professional penetration testers simulate attacks on your AD environment. These tests can uncover misconfigurations, unpatched servers, and other weaknesses before a real attacker does. In our infrastructure penetration tests,
For the best results, consider moving to a continuous testing model rather than a one-and-done yearly audit. For instance, OP Innovate’s WASP platform combines ongoing penetration testing with attack surface management, enabling organizations to constantly discover, assess, and remediate vulnerabilities in their internal and external exposure.
Protect Your AD With OP Innovate
OP Innovate offers specialized penetration testing services delivered through our continuous security testing platform, WASP, to help you identify and remediate Active Directory vulnerabilities before they can be exploited.
WASP combines the manual expertise of CREST-certified and experienced professionals with the efficiency of automation to continuously uncover, assess, and help remediate vulnerabilities across your Active Directory environment.
Get in touch with us to schedule a comprehensive infrastructure penetration test or to learn how the WASP platform can provide continuous protection for your critical assets.










